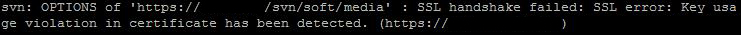
How to fix the “SSL handshake failed: Key usage violation in certificate has been detected” error on CentOS, commonly caused by GnuTLS-linked Subversion clients and self-signed certificates.
SSL handshake failed: SSL error: Key usage violation in certificate has been detected CentOS
Overview
SSL handshake failed: SSL error: Key usage violation in certificate has been detected.
Fix
You may experience the issue if both of the following conditions are met:
- VisualSVN Server has a self-signed certificate applied and
- Subversion client is built against the GnuTLS library.
GnuTLS library is an open-source alternative to OpenSSL. Most Subversion clients for Windows are built against OpenSSL and are not affected by this issue. While some Subversion packages (available mostly on Linux-based operating systems - The subversion that comes with EL 6 is linked against GnuTLS which is a change from older releases which linked against OpenSSL) are built against GnuTLS and are affected.
The server is using an SSL cert was created with the ‘key usage’ extension, and the client is using the gnutls SSL library which doesn’t understand the extension. The solution is either to have the client use the openssl library or to have the server use a cert that doesn’t use the ‘key usage’ extension.
It’s recommended to fix the issue on your server side, but you can workaround it from the client side too.
Fix (Server side)
Here is what visualsvn.com say:
It’s not recommended to use a self-signed certificate in a production environment. We advise to use a certificate issued by your domain or a third-party certificate authority instead of a self-signed one.
If you have to use a self-signed certificate please follow the instruction to generate a cerificate without specifying ‘Key Usage’ extension:
Add the following registry value to the Windows registry:
for 32-bit system:
[HKEY_LOCAL_MACHINE\SOFTWARE\VisualSVN\VisualSVN Server] “CreateGnuTLSCompatibleCertificate”=dword:00000001
for 64-bit system:
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\VisualSVN\ VisualSVN Server] “CreateGnuTLSCompatibleCertificate”=dword:00000001
Start VisualSVN Server Manager. Go to Action | Properties | Certificate. Click Change certificate… and follow the wizard instructions to generate a new self-signed certificate.
The certificate will be generated without the ‘Key Usage’ extension and will be compatible both with GnuTLS and OpenSSL.
Fix (Client side)
The options for client side fix are:
- You could building subversion from the source code and using openssl instead of gnutls in the configuration.
- Upgrading to Subversion >=1.6.16 (CentOS repo has v1.6.11 for the time being).
That’s it.
